Researchers Break Through Intel’s Security Wall
Researchers Break Through Intel SGX, Intel’s Security Wall
HAIFA, ISRAEL (August 15, 2018) – Technion-Israel Institute of Technology researchers and their colleagues abroad have broken through Intel’s innovative security wall, Intel Software Guard Extension (SGX). SGX is a recently introduced security feature of Intel processors for protecting the privacy and integrity of information and applications on the computer. It is available in all recent Intel processors and is broadly deployed in both personal computers and cloud computing services.
The attack, dubbed Foreshadow, exploits certain weaknesses in the existing mechanisms of Intel CPUs, allowing an attacker to expose private application data and forge computations secured by SGX.
The researchers reported Foreshadow to Intel in January of 2018. Further analysis into the causes of Foreshadow performed by Intel revealed that the same hardware flaw enables a number of other devastating attacks. Called Foreshadow –NG, these attacks put in risk the privacy of users of cloud computing systems that use Intel CPUs. The patches that mitigate these attacks have already been released.
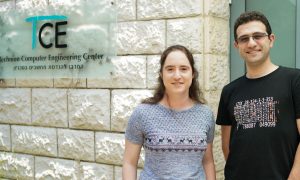
The researchers from the Technion are Assistant Prof. Mark Silberstein of the Viterbi Faculty of Electrical Engineering and his graduate student Marina Minkin from the Computer Science Department. They conducted the study together with their colleagues from The University of Adelaide (Australia), The University of Michigan (USA) and KU Leuven (Belgium). Former Technion graduates Ophir Weiss and Assistant Prof. Daniel Genkin were also involved in the research. The team’s work will be presented today (August 15, 2018) at the leading security conference, USENIX Security ’18, in Baltimore, Maryland.
SGX is a revolutionary hardware technology that enables the creation of secure execution environments, called secure enclaves. According to Prof. Silberstein, SGX has a wide range of potential applications. “Let’s say a company such as Netflix is interested in guaranteeing that its customers may watch movies only via Netflix’s own video streaming application to prevent illegal copies of the streamed contents. How to ensure that the client does not hack into the application, dumps its memory, or replaces it with a reverse-engineered version, given that the computer is entirely under her control?”
With SGX, Netflix servers can verify that the client application is invoked in a secure enclave that runs genuine Netflix software, and only then start transferring the movie. Moreover, SGX automatically encrypts all the information in the enclave’s memory with a unique key hardware-protected key. “This way, only the Netflix client, and no other applications on the computer, not even a computer administrator, may access the movie in the computer’s memory, as long as the processor hardware itself is not compromised.” SGX is also useful for cloud computing systems that rent remote computers by the hour because SGX allows their users to trust the computations performed on remote cloud computers as if they were their own. Therefore, leading cloud computing vendors including IBM, Google, and Microsoft have already announced products that rely on SGX.
But the Foreshadow attack breaks these essential SGX security guarantees.
Researchers managed to read all the information stored in the enclave – the information that the user assumes is confidential. Moreover, Foreshadow compromised the secure storage mechanisms upon which the mechanism for validating the authenticity of a remote enclave is built, enabling the researchers to forge the programs running in the enclave. In other words, Foreshadow compromises core security guarantees provided by SGX, toppling large part of the entire SGX ecosystem by exploiting a single critical hardware vulnerability.
Dr. Daniel Genkin and Dr. Yuval Yarom, two of the researchers who discovered Foreshadow, were also involved in the discovery of the Spectre and Meltdown vulnerabilities that rocked the world in January 2018. That disclosure required Intel to distribute security updates to about 90% of the processors it had sold over the past five years. Foreshadow is a Meltdown-style attack too – the first such attack on Intel SGX.